The Home of the Security Bloggers Network
Home » Cybersecurity » Application Security » How contact forms can be exploited to conduct large scale phishing activity?
A contact form for customer inquiries is one of the most common features present on the websites of most companies. It provides an easy way for prospective customers to get in touch with the company.
WordPress’ plugins are available that can help you create such functionality in a simple way. Some companies go beyond and acknowledge the message received from the customers.
During the application security assessment for one of our clients, we came across a Contact Us form that looked like the following image: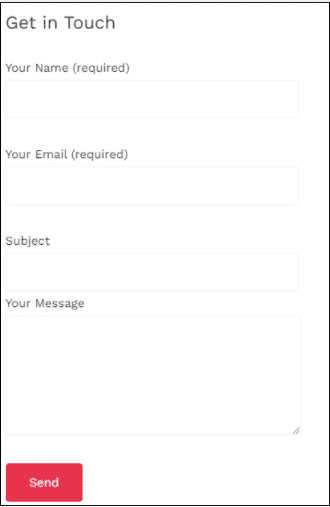
At first glance, the form seems pretty standard and harmless, but just out of curiosity, we entered data and sent our query. We entered the data in the fields as shown below: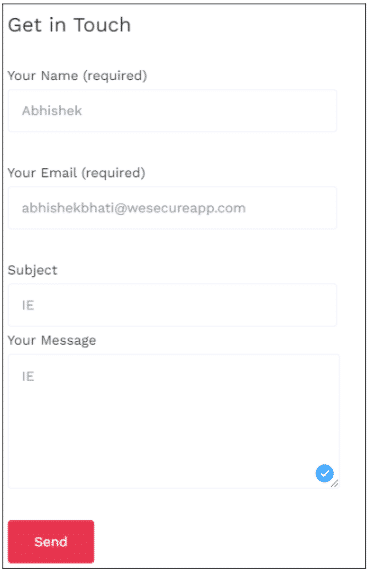
Almost instantly after this, we received a reply from the company, as depicted in the image below: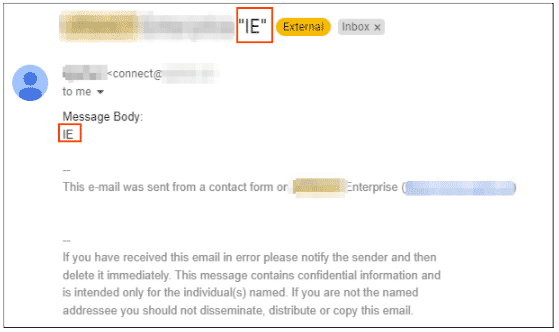
We then checked if there was any system in place to verify whether the user entering the details actually owns the email ID being entered. Turns out, there wasn’t.
On further investigation, it was found that the number of emails that can be sent weren’t limited to. A POC for how this can be exploited by an attacker is shown in the image below: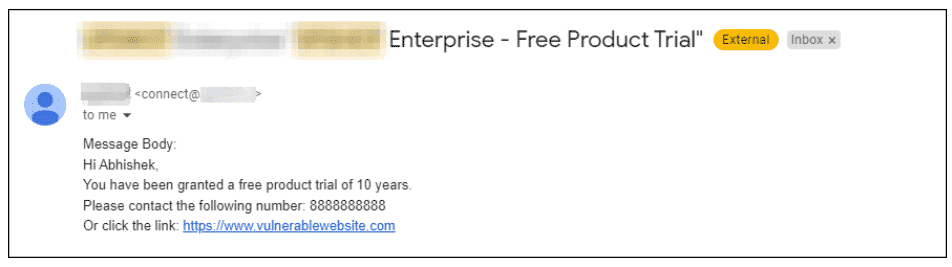
From the above email, it can be seen that without any restrictions, the attacker can redirect the user to any vulnerable link.
Furthermore, the attackers also don’t have to set up their own phishing infrastructure. They also don’t have to spend effort on account takeover of legit emails that is normally done in the email reply chain. Since the email is coming from the domain of a company that already has a reputation and proper records in place, the chances of the email landing in SPAM also turn out to be very low. With careful planning regarding the timing and crafting a highly enticing content, a large-scale phishing campaign can be conducted with the help of this form with a high degree of decisiveness.
Even in Red Teaming Activities, such forms which are often ignored by the companies from a security perspective are leveraged to conduct large scale phishing attacks. Credentials can also be harvested in a very precise manner with such vulnerable forms to employees and other related people of the company. In addition, these can often provide entry points to the customer accounts of the targeted organization.
There can be several possible ways:
For example, instead of
Message Body:
Hi ABC,
You have received a product trial.
The reply email can contain a message with much more clarity:
We received an enquiry on our website where your contact email was submitted. The
message received was as follows.
Hi ABC,
You have received a product trial.
Thanks for reaching out to us. We will contact you shortly. However, if you did not
submit an enquiry, please report it on this link: www.reporting-link.com.
A simple message like the following can be sent for acknowledgement:
Subject: XYZ Enterprise Query
Message Body:
Hi ABC,
This is an acknowledgement for the form filled by you on the enquiry section of our website
(www.xyz-enterprise.com).
Thanks for reaching out to us. We will contact you shortly. However, if you did not
submit an enquiry, please report it on this link: www.reporting-link.com.
Test your organization’s resilience against modern phishing activity – Contact Us
Moreover try our new product Strobes which is a one-stop-shop solution for all security stakeholders to ensure that their enterprise is well guarded against security issues and cyber attacks.
Abhishek Bhati
Jr.Security Analyst – WeSecureApp
The post How contact forms can be exploited to conduct large scale phishing activity? appeared first on WeSecureApp :: Simplifying Enterprise Security!.
*** This is a Security Bloggers Network syndicated blog from WeSecureApp :: Simplifying Enterprise Security! authored by Abhishek Bhati. Read the original post at: https://wesecureapp.com/blog/how-contact-forms-can-be-exploited-to-conduct-large-scale-phishing-activity/
document.getElementById( “ak_js_1” ).setAttribute( “value”, ( new Date() ).getTime() );
More Webinars